Madhu Akula - A Practical Approach to Breaking & Pwning Kubernetes Clusters $2,800 (Early $2,600)
Name of Training:
A Practical Approach to Breaking & Pwning Kubernetes Clusters
Description:
Tactics, Techniques, and Procedures (TTPs) to attack and assess Kubernetes clusters environments at different layers.
Training description:
The adoption of Kubernetes use in production has increased to 83% from a survey by CNCF. Still, most security teams struggle to understand these modern technologies.
In this real-world scenario-based training, each participant will be learning Tactics, Techniques, and Procedures (TTPs) to attack and assess Kubernetes clusters environments at different layers like Supply chain, Infrastructure, Runtime, and many others. Starting from simple recon to gaining access to microservices, sensitive data, escaping containers, escalating to clusters privileges, and even its underlying cloud environments.
By end of the training, participants will be able to apply their knowledge to perform architecture reviews, security assessments, red team exercises, and pen-testing engagements on Kubernetes Clusters and Containersed environments successfully. Also, the trainer will provide step by step guide (Digital Book) with resources and references to further your learning.
Trainer(s) bio:
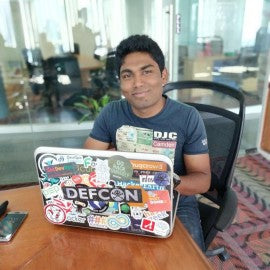
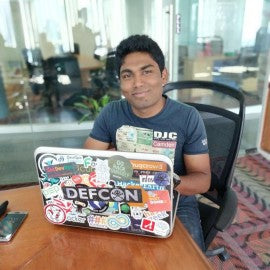
Madhu Akula is a pragmatic security leader and creator of Kubernetes Goat, an intentionally vulnerable by design Kubernetes Cluster to learn and practice Kubernetes Security. Also published author and Cloud Native Security Architect with extensive experience. Also, he is an active member of the international security, DevOps, and Cloud Native communities (null, DevSecOps, AllDayDevOps, AWS, CNCF, USENIX, etc). He holds industry certifications like CKA (Certified Kubernetes Administrator), CKS (Certified Kubernetes Security Specialist), OSCP (Offensive Security Certified Professional), etc.
Madhu frequently speaks and runs training sessions at security events and conferences around the world including DEFCON 24, 26, 27, 28, 29 & 30, BlackHat 2018, 19, 21 & 22, USENIX LISA 2018, 19 & 21, SANS Cloud Security Summit 2021 & 2022, O’Reilly Velocity EU 2019, Github Satellite 2020, Appsec EU (2018, 19 & 22), All Day DevOps (2016, 17, 18, 19, 20 & 21), DevSecCon (London, Singapore, Boston), DevOpsDays India, c0c0n(2017, 18), Nullcon 2018, 19, 21 & 22, SACON, Serverless Summit, null and multiple others.
His research has identified vulnerabilities in over 200+ companies and organizations including; Google, Microsoft, LinkedIn, eBay, AT&T, WordPress, NTOP, Adobe, etc. and is credited with multiple CVE’s, Acknowledgements, and rewards. He is co-author of Security Automation with Ansible2 (ISBN-13: 978-1788394512), which is listed as a technical resource by Red Hat Ansible. He is the technical reviewer for Learn Kubernetes Security, Practical Ansible2 books by Packt Pub. Also won 1st prize for building an Infrastructure Security Monitoring solution at InMobi flagship hackathon among 100+ engineering teams.
Trainer(s) social media links:
https://twitter.com/madhuakula
https://www.linkedin.com/in/madhuakula/
https://github.com/madhuakula
Previous content:
Blackhat
- USA https://www.blackhat.com/us-21/training/schedule/#a-practical-approach-to-breaking--pwning-kubernetes-clusters-22130
- EU https://www.blackhat.com/eu-21/training/schedule/#a-practical-approach-to-breaking--pwning-kubernetes-clusters-24396
- Asia https://www.blackhat.com/asia-22/training/schedule/#a-practical-approach-to-breaking--pwning-kubernetes-clusters-25190
- EU https://www.blackhat.com/eu-22/training/schedule/index.html#a-practical-approach-to-breaking--pwning-kubernetes-clusters-28037
DEF CON TRAININGS LV 2022
Outline:
Section-1:
* Kubernetes 101 - Fasttrack Edition
* Security Architecture review & Attack Trees using MITRE ATT&CK framework
* `kubectl` kung-fu to explore the cluster
* Attacking the supply chain by exploiting private registry
* Pwning the container images and gaining access to the cluster
* Exploiting security misconfigurations in the cluster
Section-2:
* Escaping out of the container to the host system to gain more privileges
* Bypassing NSP and gaining unauthorized access to other microservices
* Lateral movement from container to node and then complete cluster access
* Escalating from ServiceAccount to more RBAC privileges (No least privileges)
* Helm with Tiller service = ClusterPwn (Complete cluster takeover)
* Gaining access to k8s volumes, logs of the services, and sensitive data
* From application vulnerability to cloud provider access (attack chain)
Section-3:
* Hacker Container - The Swiss Army knife for hacking Kubernetes Clusters
* Exploiting Kubernetes Secrets and gaining access to third-party services
* DoS the services and cluster nodes by resources exemption
* Understanding Admission controller and possible attack surface around Webhooks
* Persisting in the clusters using Sidecar/Cronjob/DaemonSets
* Defense evasion techniques for Kubernetes Cluster environments
* Some useful hacks around `kubectl` (cheatsheet will be provided)
Section-4:
* Tools, and techniques beyond manual exploitation and analysis
* KubeAudit, KubeSec, popeye, trivy, dockle, rakkess, linters, and many others...
* Performing Docker & K8S CIS benchmarks to find all the possible security risks
* Auditing the cluster security posture from Code to Production running cluster
* Real-World case studies of Kubernetes Hacking, Vulnerabilities, and Exploits
* Best practices, Recommendations based on the Security Maturity
* Resources & references to further your attacks, exploitation, more learning
Technical difficulty:
Intermediate
- Able to use Linux CLI
- Basic understanding of system administration
- Experience with Docker and Containers ecosystem would be useful
- Security Experience would be plus
Suggested Prerequisites:
My DEFCON 26 workshop on Attacking & Auditing Docker Containers Using Open Source tools and its video available at https://www.youtube.com/watch?v=ru7GicI5iyI
What students should bring:
Students will need a laptop with Wi-Fi capability.
I will be providing students with
- Custom built Kubernetes Cluster environment (everyone gets their own)
- Step by Step Digital Guide book for the entire training
- Kubectl cheatsheet, Checklist of tools, and other resources
DATE: November 2nd-3rd 2024
TIME: 8am to 5pm PDT
VENUE: Meydenbauer Center, Bellevue, WA
TRAINER: Madhu Akula
- 16 hours of training with a certificate of completion.
- 2 coffee breaks are provided per day
- Note: Food is not included
Registration terms and conditions:
Trainings are refundable before September 16th, the processing fee is $250.
Trainings are non-refundable after September 26th, 2024.
Training tickets may be transferred. Please email us for specifics.
Failure to attend the Training without prior written notification, will be considered a No-Show. No refund will be given.
By purchasing this ticket you agree to abide by the DCT Code of Conduct and the registration terms and conditions listed above.
